In September 2019, the Safari WebKit team announced Intelligent Tracking Prevention (ITP) 2.3. While it has had a smaller direct impact versus previous ITP releases, Safari ITP 2.3 contains important lessons for marketers and their technology teams, not just in narrow terms of cookie strategy, but in more broad-reaching terms that beg a fundamental shift in how brands approach digital marketing and advertising.
Safari ITP 2.3 Thwarts More Tracking Workarounds
The incremental updates in Safari ITP 2.3 are intended to thwart a few workarounds and mitigation tactics that advertisers, publishers, and tech platforms were using. Some workarounds were employing localStorage or using the JavaScript Document.referrer property. The Safari WebKit team identified the scenarios where these tactics could be used to circumvent Safari's tracking prevention features and took steps to close the gaps. You can read the full ITP 2.3 release notes here.
The takeaway is that Apple and Safari will move quickly to shut down practices that they deem in violation of their concept of user privacy and security.
The Last Fallback: First-party HttpOnly Cookies
Safari ITP 2.3 still allows unlimited expiration for all cookies set server-side, regardless of the HttpOnly attribute. But the Safari team is already clarifying that only server-side cookies using the HttpOnly attribute are truly secure:
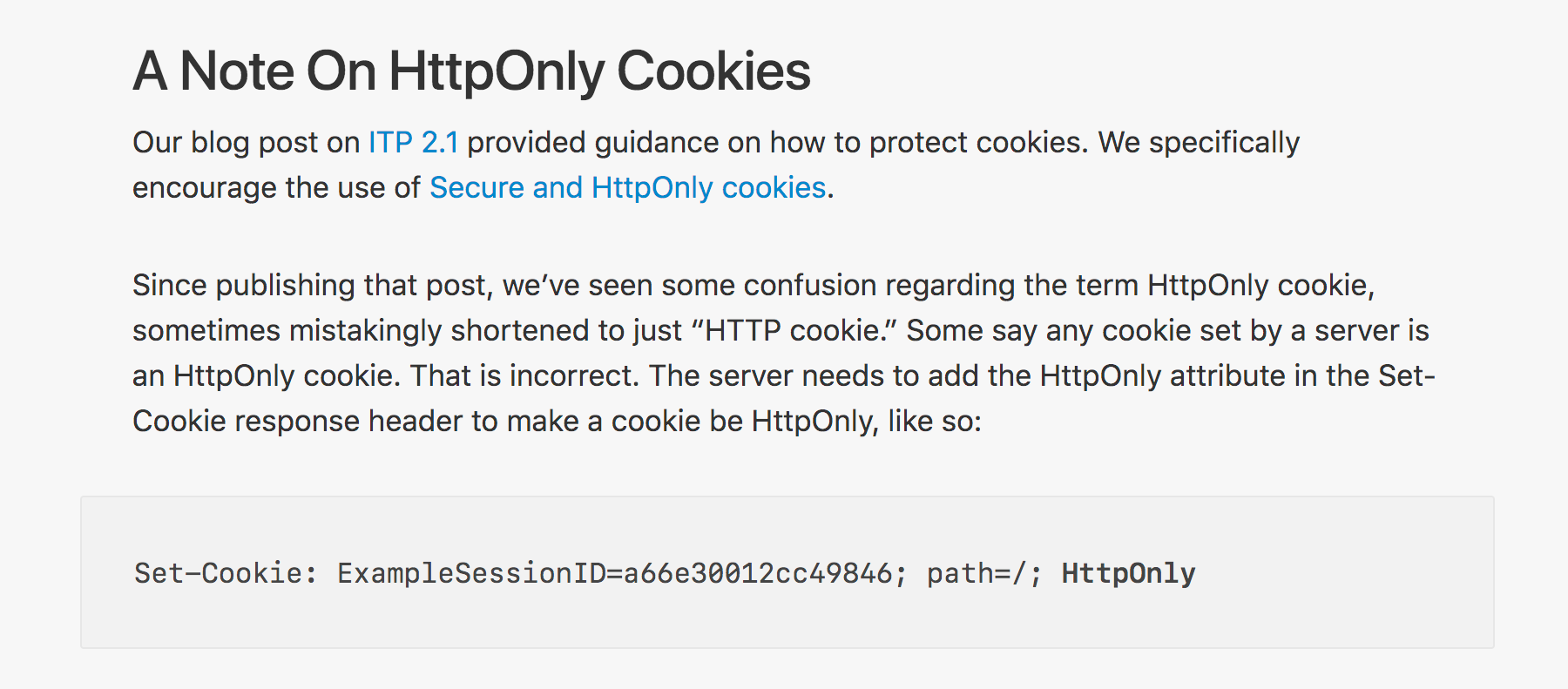
Source: Webkit.org
In the past, the Safari WebKit team has referenced an article by Google Engineer Mike West. The article cites a low 8.31% adoption rate of server-side cookies using the HttpOnly attribute as a security issue. In reiterating this concern with the latest ITP release, the Safari WebKit team is painting a clear picture. This should be taken as a not-so-subtle hint about your cookie strategy to favor the HttpOnly attribute.
It should also reinforce a larger lesson for marketers regarding ITP: the goal should not be to find temporary, short-term work-arounds. These efforts (which are often burdensome) will likely yield few sustainable results.
This is About More Than Cookies
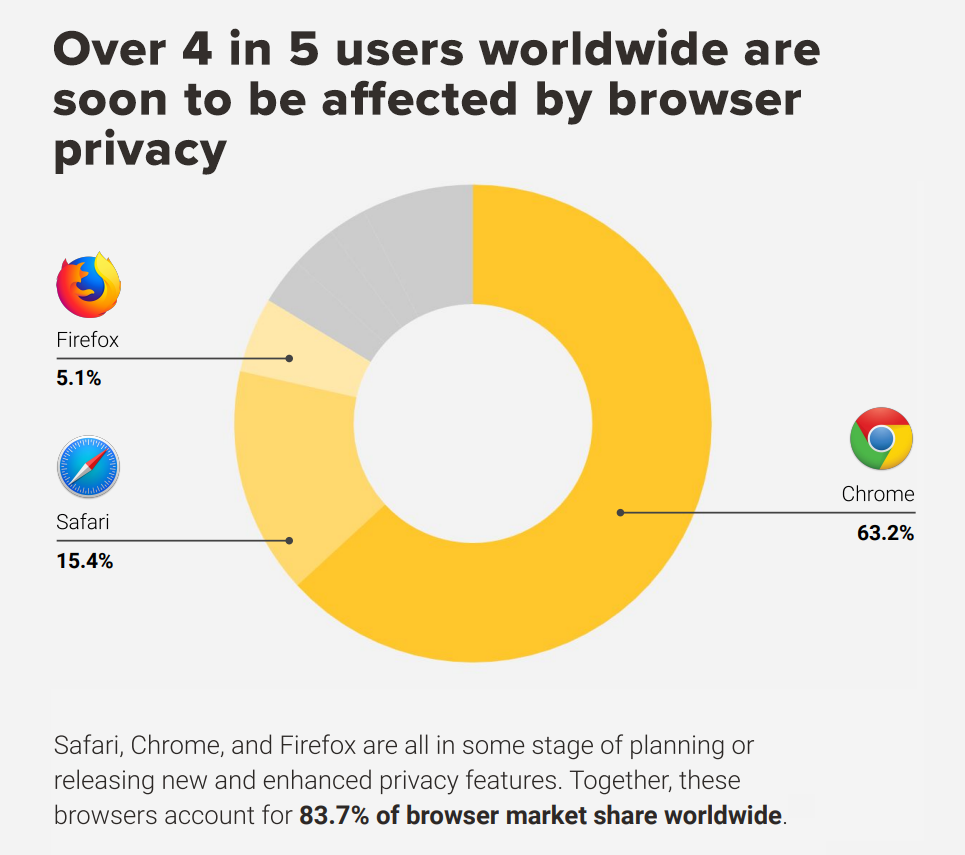
Privacy is here to stay, and advertisers will need to adapt their thought process as much as their technology. Safari ITP should be seen as a part of a broader push for user privacy and security across the web, and it is much easier to understand if seen in this light.
Source: "Digital Privacy in a Post-Cookie World"
Trying to "work around" or "solve for" Safari ITP (or GDPR and CCPA for that matter), or insisting on 1:1 user mapping rather than working from larger (but still actionable and measurable) audience cohorts is a misguided path. Advertisers should mitigate the effects of Safari ITP where possible, but keep focus on developing more durable privacy-safe strategies around first-party data, user logins, universal first-party IDs, opt-ins, and data clean room technology. Soon, advertisers won't be able to execute tactics that may have worked just a year ago. Fighting this change will just keep get harder and yield fewer results as time goes by.
With all the clear indicators of where things are heading, not changing your approach to privacy is akin to polishing your saddle rather than learning how to drive a car.
How will the shift to digital privacy affect digital marketers?
Download our report "Digital Privacy in a Post-Cookie World" to understand how privacy trends will impact marketers and learn about possible solutions.